“This debate is quite polarizing; it’s been in the media for a couple of years now. It was quite an accomplishment on our part to agree on a set of facts, to agree on a vocabulary and to agree on the framework.” — Fred Chang, SMU
Journalist Justin Martin with KERA public radio covered the new government guidelines for investigating encrypted data from the National Academies of Sciences, Engineering and Medicine. Frederick Chang, director of SMU’s Darwin Deason Institute for Cyber Security and former director of research for the National Security Agency, participated in developing the guidelines.
KERA’s interview, “8 Questions For The Government To Consider Before Investigating Encrypted Data,” aired March 7, 2018.
Chang, a member of the prestigious National Academy of Engineering, joined SMU in September 2013 as Bobby B. Lyle Endowed Centennial Distinguished Chair in Cyber Security, computer science and engineering professor and Senior Fellow in the John Goodwin Tower Center for Political Studies in Dedman College. The Darwin Deason Institute for Cyber Security was launched in SMU’s Lyle School of Engineering in January 2014, with Chang named as its director.
In addition to his positions at SMU, Chang is a distinguished scholar in the Robert S. Strauss Center for International Security and Law at the University of Texas at Austin. Chang has been professor and AT&T Distinguished Chair in Infrastructure Assurance and Security at the University of Texas at San Antonio and he was at the University of Texas at Austin as an associate dean in the College of Natural Sciences and director of the Center for Information Assurance and Security. Additionally, Chang’s career spans service in the private sector and in government including as the former Director of Research at the National Security Agency.
Chang has been awarded the National Security Agency Director’s Distinguished Service Medal and was the 2014 Information Security Magazine ‘Security 7’ award winner for Education. He has served as a member of the Commission on Cyber Security for the 44th Presidency and as a member of the Computer Science and Telecommunications Board of the National Academies. He has also served as a member of the National Academies Committee on Responding to Section 5(d) of Presidential Policy Directive 28: The Feasibility of Software to Provide Alternatives to Bulk Signals Intelligence Collection.
He is the lead inventor on two U.S. patents, and he appeared in the televised National Geographic documentary, Inside the NSA: America’s Cyber Secrets. He has twice served as a cyber security expert witness at hearings convened by the U.S. House of Representatives Committee on Science, Space and Technology.
Chang received his B.A. degree from the University of California, San Diego and his M.A. and Ph.D. degrees from the University of Oregon. He has also completed the Program for Senior Executives at the Sloan School of Management at the Massachusetts Institute of Technology.
Listen to the KERA radio interview with Justin Martin.
EXCERPT From KERA News:
The debate over government access to personal and private information dates back decades. But it took center stage after the 2015 mass shooting in San Bernardino, California, when Apple refused to open a backdoor into an assailant’s encrypted cell phone for FBI investigators.
The agency ultimately paid a hacker to unlock the phone instead.
Now, the National Academies of Sciences, Engineering, and Medicine has produced a set of guidelines for government agencies to consider before approaching or investigating encrypted data.
To learn more about them, I talked with Frederick Chang, the executive director of Southern Methodist University’s Darwin Deason Institute for Cyber Security.
He’s also a member of the National Academy of Engineering and former director of research for the National Security Agency.





 Top Quark: New precise particle measurement improves subatomic tool for probing mysteries of universe
Top Quark: New precise particle measurement improves subatomic tool for probing mysteries of universe New fossils intensify mystery of short-lived, toothy mammals unique to ancient North Pacific
New fossils intensify mystery of short-lived, toothy mammals unique to ancient North Pacific Drugs behave as predicted in computer model of key protein, enabling cancer drug discovery
Drugs behave as predicted in computer model of key protein, enabling cancer drug discovery Researchers discover new drug-like compounds that may improve odds for men battling prostate cancer
Researchers discover new drug-like compounds that may improve odds for men battling prostate cancer Fermilab experiment observes change in neutrinos from one type to another over 500 miles
Fermilab experiment observes change in neutrinos from one type to another over 500 miles Large genome-scale study finds Native American ancestors arrived in single migration wave
Large genome-scale study finds Native American ancestors arrived in single migration wave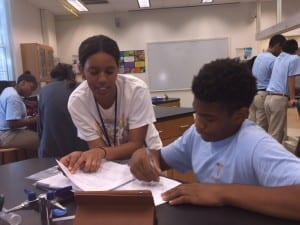 $3.78 million awarded by Department of Defense to SMU STEM project for minority students
$3.78 million awarded by Department of Defense to SMU STEM project for minority students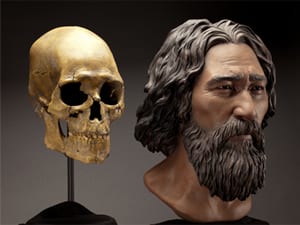 Kennewick Man: genome sequence of 8,500-year-old skeleton solves scientific controversy
Kennewick Man: genome sequence of 8,500-year-old skeleton solves scientific controversy At peak fertility, women who desire to maintain body attractiveness report they eat less
At peak fertility, women who desire to maintain body attractiveness report they eat less SMU seismology team to cooperate with state, federal scientists in study of May 7 Venus, Texas earthquake
SMU seismology team to cooperate with state, federal scientists in study of May 7 Venus, Texas earthquake 1st proton collisions at the world’s largest science experiment expected to start the first or second week of June
1st proton collisions at the world’s largest science experiment expected to start the first or second week of June Most likely cause of 2013-14 earthquakes: Combination of gas field fluid injection, removal
Most likely cause of 2013-14 earthquakes: Combination of gas field fluid injection, removal
